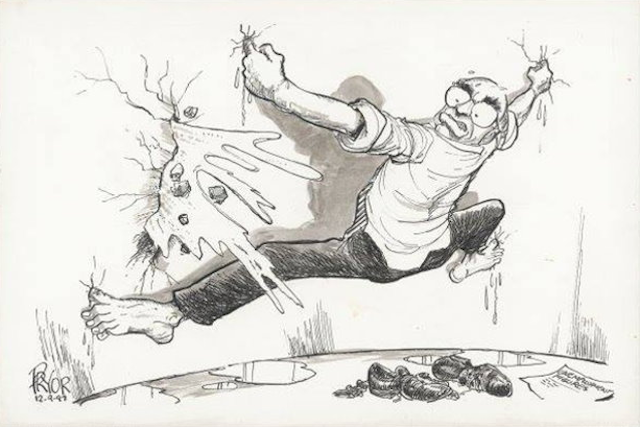
This week, in recognition of Data Privacy Week (Jan. 24 – 28), my colleague Tina Simpson wrote about the current state of legal protection within the United States for protecting and ensuring our individual data privacy. Not surprisingly, the mishmash of federal protections supplemented by state legislation creates an image in my mind of frantically trying to plug leaks in a breaking dam
(for an illustration of the panic that comes with this doomed task, see Geoff Pryors cartoon) 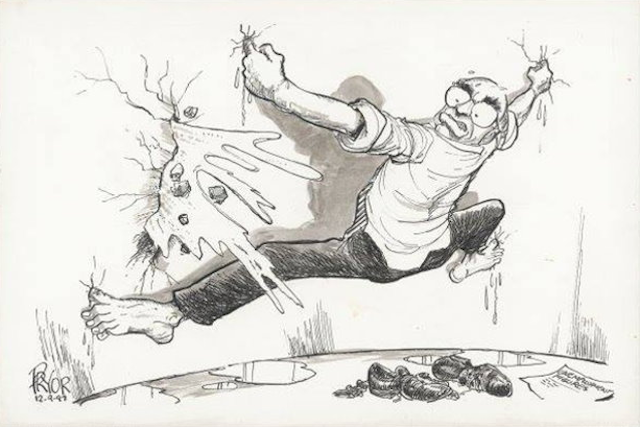
As a business owner, ensuring that we are not asking for and holding on to more data than is absolutely necessary from team members, vendors, and clients is a priority. There are contract requirements, laws and regulations, insurance requirements, and so on that provide me with a guide (of sorts) on how to limit data requests and how we store, maintain, and protect that data. Sometimes overwhelming, sure. But, super helpful. Because at least there are instructions that I can follow.
You know what I didn’t get though when I had my son? Similar guides and directions on how to protect his data privacy. And so, Parents, this article is for you.
The onus to protect your child’s data privacy is in fact on you because we do not have a privacy by design structure in the United States. That means companies do not have an obligation to ensure the privacy and protection of your and your children’s data unless they and you are covered by one of the, few, slap-dash laws that we have. I use the term “slap-dash” advisedly. And even then, they must only follow the letter of the law, which often leaves significant wiggle room.
Parenting in the Digital Age
As a parent, I have said, more than once, I have no idea how my parents survived raising two children without the benefit of technology. Let me give two examples that I am sure many parents will relate to.
- Problem: Out to dinner with my toddler and in desperate need of adult conversation with my husband. Solution: Hand my iPhone to my son so he could play some game and be distracted for 10 minutes.
- Problem: COVID hits and we are all isolating for months. How to mitigate the consequences of such isolation for my 8-year-old? Solution: Set up FaceTime and text messaging for him to be in touch with his friends and allow him to begin playing online games so that he can have some way to “play” with his friends. Relatedly, as my son attempted to complete 3rd grade remotely (insert hysterical laughter here), I relied on YouTube to remind me how to convert fractions and find the area of a quadrilateral (after first googling what a quadrilateral is).
We have definite limitations in place in our house though. No Facebook, Twitter, TikTok, Instagram, or other social media. He isn’t allowed to post videos online, such as on YouTube, and he isn’t permitted to watch YouTube unsupervised. Yet, he is still exposed to these because his peers do have access and use of social media and host their own YouTube channels.
These restrictions are certainly a source of contention in our house. “Why can’t I have an Instagram account? “(Insert friend’s name here) has one.” When that timeless argument proved unsuccessful, guess who tried to set one up on his own? Yep, like his mom, he’s not real big on having people tell him he can’t do something. How’d we find out? We checked. We regularly check his devices to see what he’s been up to. We also get alerts because our accounts are linked through Family Accounts.
Much to our son’s dismay, his father is a privacy and security professional. So, in house, performing forensic analysis on information technology is not difficult. That said, it is important for all parents to understand you don’t have to be an IT wiz or expert to keep your kids safe.
Technology is a blessing and a curse. It opens tremendous positive opportunities, such as maintaining important relationships when distance or other reasons would potentially get in the way, it expands learning opportunities, it makes things easier by increasing the convenience of things, and it provides a mechanism for parents to “keep an eye” on our children when they aren’t directly in front of us, lending credence to another age-old parental expression that “I have eyes in the back of my head.” It also has the potential to be incredibly dangerous. Here are just a few examples:
Ensuring your child’s privacy and safety is no small task and it requires
vigilance. When a child’s data and privacy are violated, the impact isn’t always immediate or short-lived, it can have lifetime consequences. Imagine turning 18 and entering the adult world to learn that you can’t receive credit because someone stole your
identity when you were 10 and ruined your credit before you even could legally have credit.
What can we, as parents, do?
First, know what is at stake. To do this let’s begin with some definitions:
- Privacy: the state or condition of being free from being observed or disturbed by other people.
- Data: individual facts, statistics, or items of information. All activity in digital spaces creates a digital footprint, which can include personal information, or which may track back to an individual user.
- Data Privacy: The ability to exert control over how your personal information is collected, used, and disclosed.
Why is it important to define these? It’s so we understand the depth and breadth of what needs protecting. When we think about our child’s privacy and what “data” is available, it isn’t just their name, date of birth, and social security number. It is also their image, their location, where they go to school, what extracurricular activities they participate in, their thoughts and ideas.
Second, know what legal and regulatory protections currently exist.
- Federal: Children’s Online Privacy Protection Act: Creates a duty for websites tailored to children 13 years of age or younger (or where operator has knowledge of use by such minors) to protect the minors’ data and restrict data collection practices. This includes posting and maintaining a compliant privacy policy, as well as the collection of verifiable consent from parents prior to collection of personal data. Family Education Rights and Privacy Act: prevents the sharing of personal student data and educational records with third parties without parental consent, but there are exceptions that do permit such sharing with vendors and consultants.
- State: Two states (California and Delaware) have explicit child privacy acts. However, most states have some form of general privacy laws touching on the collection and protection of data.
Knowing what legal protections exist is important. But it is equally important to understand the limitations of such protections. In many cases, there are exceptions, loopholes, and just downright gaps. In other instances, there are practical issues that mitigate against actual and meaningful protection. Some of these include
social media companies’ inability to know how old a user actually is. In other cases, it’s because we have not made meaningful and significant investment in ensuring the safety of our networks, computers, smartphones, and
Internet of Things (IoT) devices in our children’s environments. For example, while
schools are subject to federal and state laws to protect children’s data, they have been and continue to be, a
preferred target of ransomware and other forms of data theft.
Third, take action to protect your children’s privacy. There are several resources that you can use to help know what steps to take. The National Cybersecurity Alliance has it’s
How to Stay Safe Online resource and Apple has recently released its
Personal Safety User Guide.
Other resources you can use to understand the digital environment our children spend so much time in, as well as to specifically engage with your children digital privacy and security include the following:
Finally, I return to the image of the breaking dam. The bottom line that I would want you to take away from this is to recognize that our regulatory structure and the business models of the digital economy mean that the steps I’ve outlined above present no guarantee of actual protection. Our regulations, such as they are, remain reactive and remedial, and there is ample evidence that that is insufficient in this growing digital ecosystem.
To quote my colleague, Tina, “
We’re moving against the current; if we want things to be different, we need to move upstream and interrupt and change that current.” It is only then that we may be able to take our fingers and toes from the dam.
Michealle Gady, JD, is Founder and President of Atromitos, LLC, a boutique consulting firm headquartered in Wilmington, North Carolina. Atromitos works with a variety of organizations from health payers and technology companies, to community-based organizations and nonprofits but their work reflects a singular mission: creating healthier, more resilient, and more equitable communities. Michealle takes nearly 20 years’ experience in health law and policy, program design and implementation, value-based care, and change management and puts it to work for Atromitos’ partners who are trying to succeed during this time of dramatic transformation within the U.S. healthcare system. Outside of leading the Atromitos team, Michealle serves as a Board Member for both the Cape Fear Literacy Council and A Safe Place and is a member of the American College of Healthcare Executives and American Health Law Association.